No matter who made your Bluetooth beacons, one fact that you can count on is that they’ve vulnerable to attack by a malicious party. Little in the past has been done to make beacons secure.
- Why should you care about beacon security?
- How can beacons be attacked and why would anyone do that?
- How do we make beacons secure?
- How to protect beacons?
How secure is your beacon infrastructure?
Download our guide to learn how to keep your infrastructure up and running.
While beacons are a fundamentally a simple technology, there are several complicated ways they can be compromised, and while many companies protect against one kind of attack or another no one has a complete solution for beacon security from beginning to end. So at Kontakt.io, we’re fixing that.
Why should you care about beacon security?
Beacon implementations are moving from pilot phase to serious businesses that involve more and more money, third parties, and information. Information that some are getting interested in.
According to Tim Parry from TechCrunch, security is the second most important thing an IoT device needs (after power enough to function at all). It’s only when you have a beacon turned on and secured that you can trust it to do its job, such as notifying users about locations, make transactions happen via secure channels, or interact with the real world around a beacon.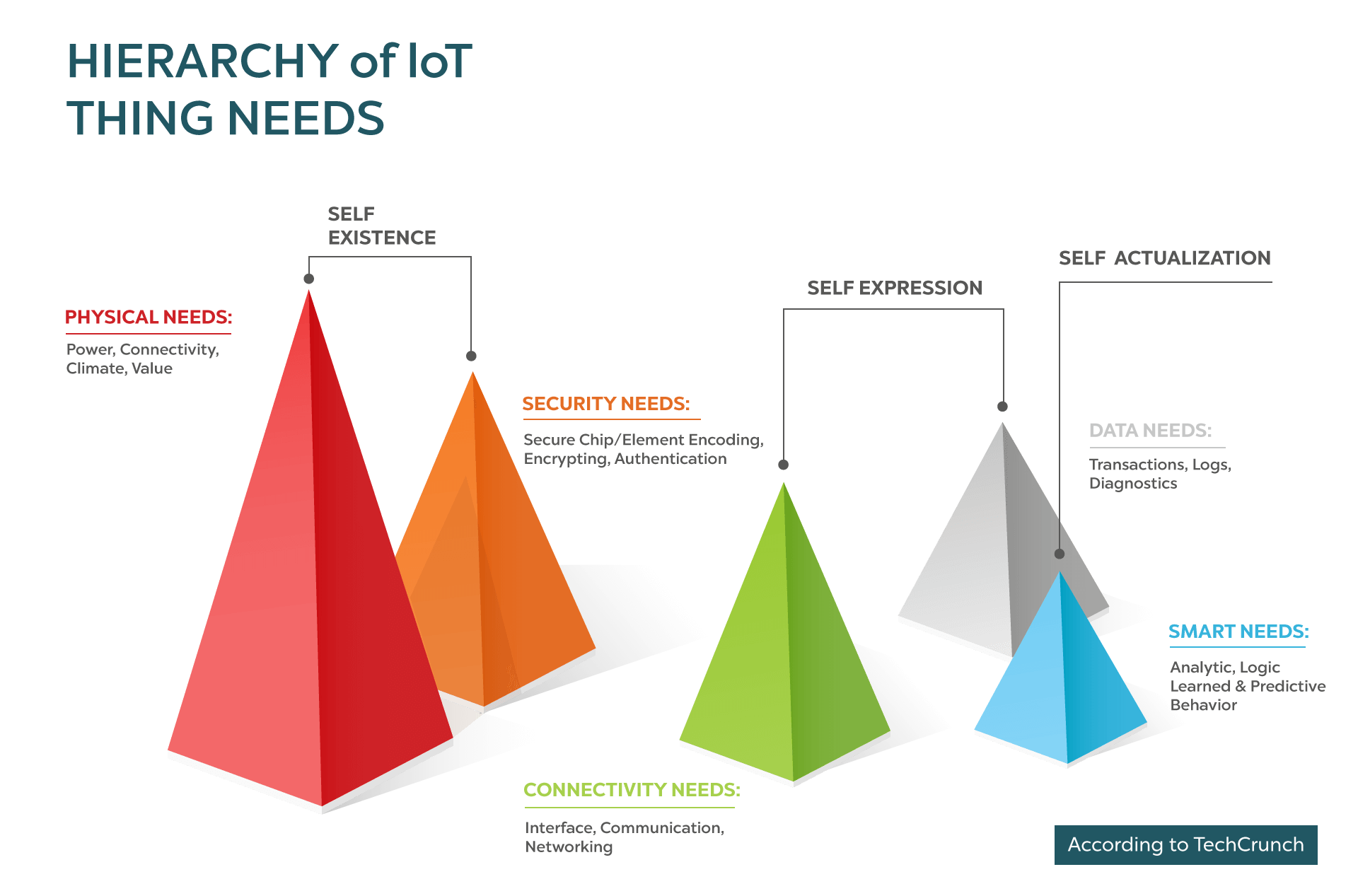
Source
If we want to push IoT forward, it’s time to protect the beacosystem.
There are four different ways your beacons can be attacked: Piggybacking, Cloning, Hijacking, and Cracking. These different types of attack require different kinds of defense, so let’s examine them in brief:
How can beacons be attacked and why would anyone do that?
A beacon is a simple device that constantly emits a radio signal. Furthermore, all communication with a beacon happens “in the clear” and isn’t encrypted. As beacons are rapidly becoming gateways to complicated interactions that have a financial motivation, there’s increasing incentive for someone to use your beacons in ways you hadn’t intended.
Piggybacking & Cloning

Piggybacking, is when an attacker listens to your beacon and captures your beacons’ UUIDs, Majors, and Minors and adds them to his or her application without your consent. Since most beacons broadcast the same signal for months and years, they can rely on your beacon infrastructure in their own app. Sharing your infrastructure for free with strangers is inconvenient, but it doesn’t damage your app or have a negative effect on your customers.
Having captured the information, your hacker may also clone your beacons, and this one is much worse. Cloning consists of copying your beacon configuration and putting it into another beacon to mislead your users. Just imagine you have a beacon triggering in-app payments–and someone else is now in control of when and where they trigger. The results could be disastrous.
Hijacking

By default, beacons communicate “in the clear” and don’t encrypt the data that is sent to them. So when you’re connecting to a beacon, someone can see the password you sent to connect to your beacon and then use it and change it, so you can’t connect anymore. The hacker, then, has a full control over your device. Your entire IoT infrastructure could be at risk from this.
Cracking

Finally, even if you’ve secured your beacon from remote attacks, you can always fall victim to someone who physically removes your beacon from the wall, opens it up, and probes the memory directly. This is a very low-probability event, since the effort involved is pretty extreme, but if you’ve got a beacon that’s controlling a door lock or other sensitive use case, there could be a big enough incentive where you need to defend against this, too.
Why hasn’t anyone fixed this? How do we make beacons secure?
The short version is: Kontakt.io is about to.
The longer version is that it’s not been fixed because it’s hard; many other companies have protected their devices from piggybacking or cloning, and chip manufacturers such as Nordic can enable defenses against cracking. But unless you’re protecting the entire chain of data, the efforts are worthless, and no one has a defense against hijacking. Yet.
Soon, we’re releasing Kontakt.io Secure, the world’s only complete suite of beacon security technology that fully protects your beacons against every kind of attack. Kontakt.io Secure will bring two new features: Kontakt.io Secure Shuffling and Kontakt.io Secure Communication. Because the technology is so brilliantly simple, these kinds of tools are the only way to make beacons secure.
Kontakt.io Secure Shuffling

It’s the industry’s most convenient and secure means to prevent someone from making a cloning attack. Shuffling changes your beacons’ Majors and Minors on a random basis, so no one can piggyback or spoof your device.
With Kontakt.io Secure Shuffling, you can set shuffling to occur on a daily basis, either individually or in bulk. Developing mobile apps with the Kontakt.io Proximity SDK, the new information that your beacon broadcasts is seamlessly syncced up, so the security is simply integrated with your application.
Kontakt.io Secure Communication

It’s the completely encrypted communication channel from a beacon to a device that manages it, so no one can hijack your beacons. Because there’s end to end encryption, there is no need to send passwords between the SDK and beacons, so it’s impossible to hijack a beacon.
Having received the Kontakt.io Secure and being managed through the Kontakt.io Proximity API or SDK, your beacons become the best-secured devices on the market and are finally well defended against the two most common attacks that a malicious person may try to exploit.
Software Lock

Since we first started shipping beacons over two years ago, we have secured them against direct cracking by enabling a software lock in the firmware for our Nordic chipset. As a result, attempting to access memory off the device results in wiping the volatile memory. While the basic beacon configuration will be available, no other information will be recoverable to a cracker, so you can rest assured that your infrastructure is safe.
What’s next – how to protect beacons?
To help protect your devices and data with dedicated end-to-end security, we’ve created a white paper where we walk you through the beacon challenges and solutions on how to keep your infrastructure safe. Download the guide now.